The IR platform that lives
inside your boundary.
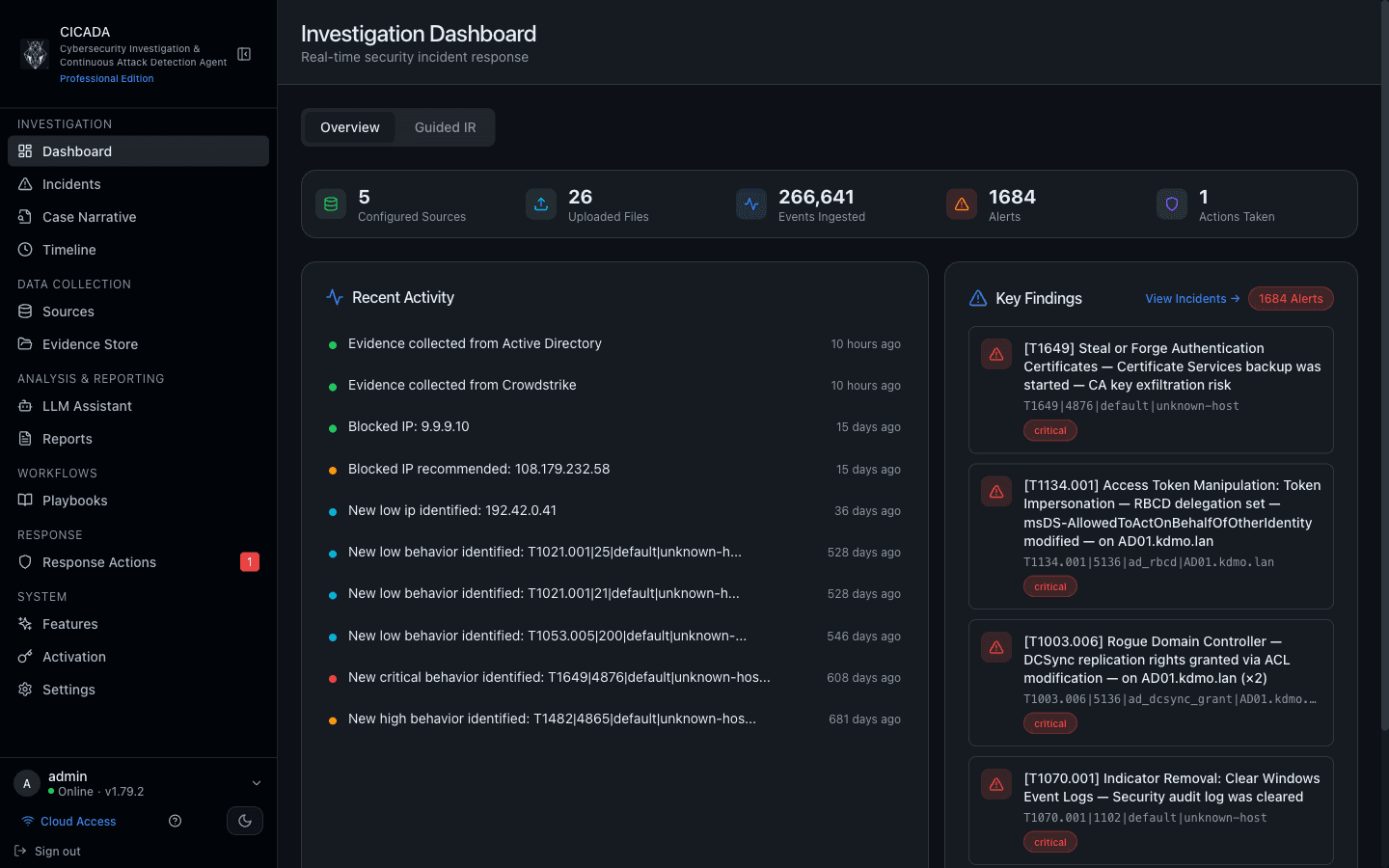
One VM. Five-stage pipeline. AI that runs on your hardware. CICADA IR replaces the five tools your team is stitching together during an incident — across Microsoft, CrowdStrike, and Active Directory environments.
During an incident, your team is in five tools at once.
Each tool sees a slice. None of them see the kill chain. You're the integration — copying IOCs between consoles, reconciling timelines, drafting the report at 2am. CICADA IR replaces that chaos with one guided workflow.
- ×Five consoles open. Five sets of credentials. Five filters.
- ×Hand-copying IOCs between vendors to enrich them.
- ×Reconstructing the timeline in a spreadsheet.
- ×AI tools that send your evidence to someone else's cloud.
- ✓One VM. One dashboard. One unified timeline.
- ✓IOCs auto-enriched against six TI sources.
- ✓Hierarchical incidents grouped by kill chain, not log volume.
- ✓Local LLM. Evidence never leaves the boundary.
Built to be deployed inside your security boundary.
We're a new vendor. We don't expect blind trust. We earn it the same way good IR works: by being explicit about every artefact we publish.
Sovereign by design
Single VM appliance inside your network. No SaaS dependency. Air-gapped activation supported.
Read-only by default
Connections to data sources are read-only. Optional response actions are explicit and audited.
Auditable everywhere
Chain of custody for every piece of evidence. Per-release SBOM. Public changelog.
Four pillars. One platform.
Every screenshot below is the actual product — no mockups.
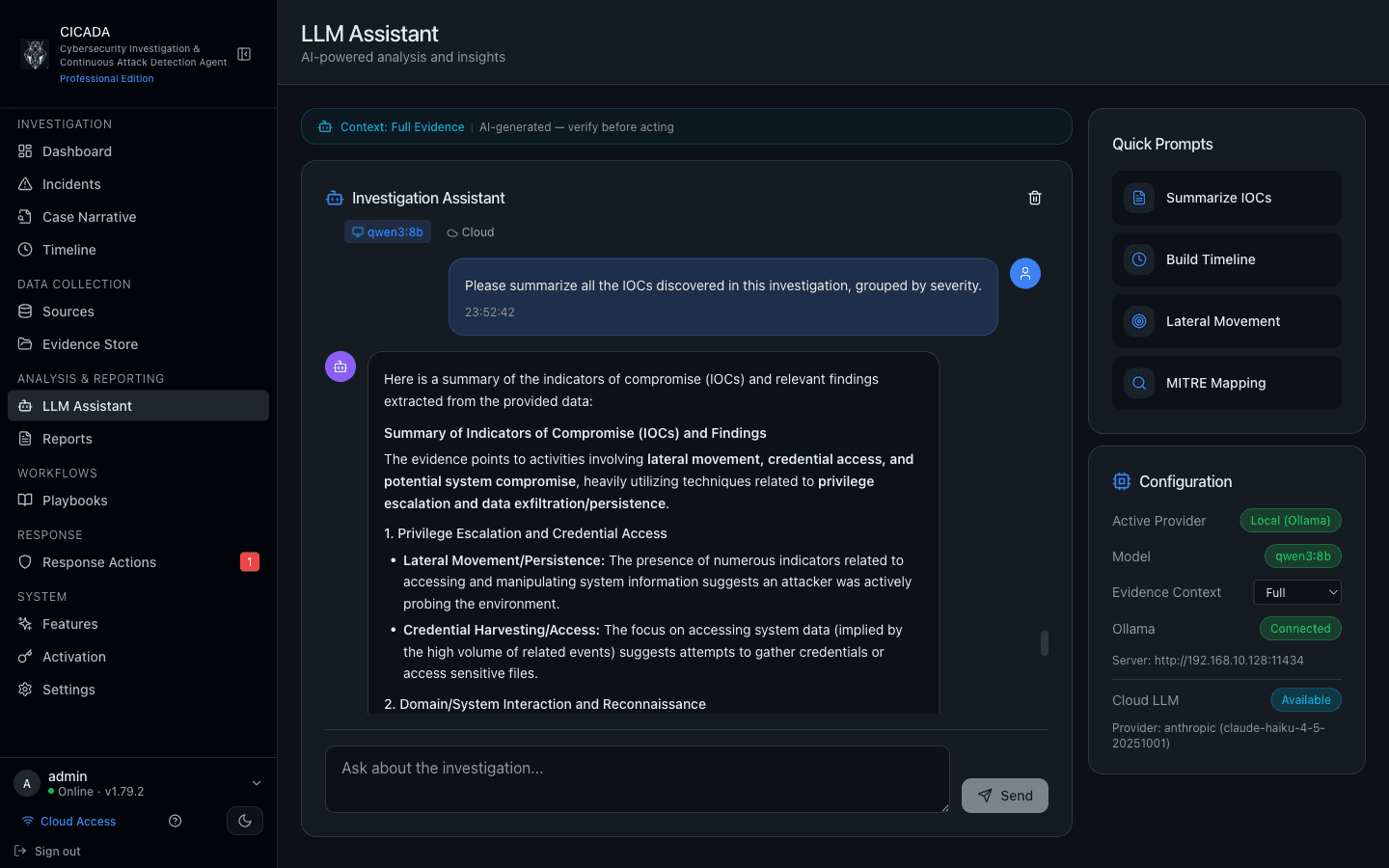
Local LLM. AI Without Leaving the Boundary.
Ollama, LM Studio, llama.cpp, or any OpenAI-compatible local proxy run end-to-end on the VM. Cloud LLMs are opt-in per-provider with PII/credential blocking and an audited "allow sensitive data" toggle.
Local LLM setup guide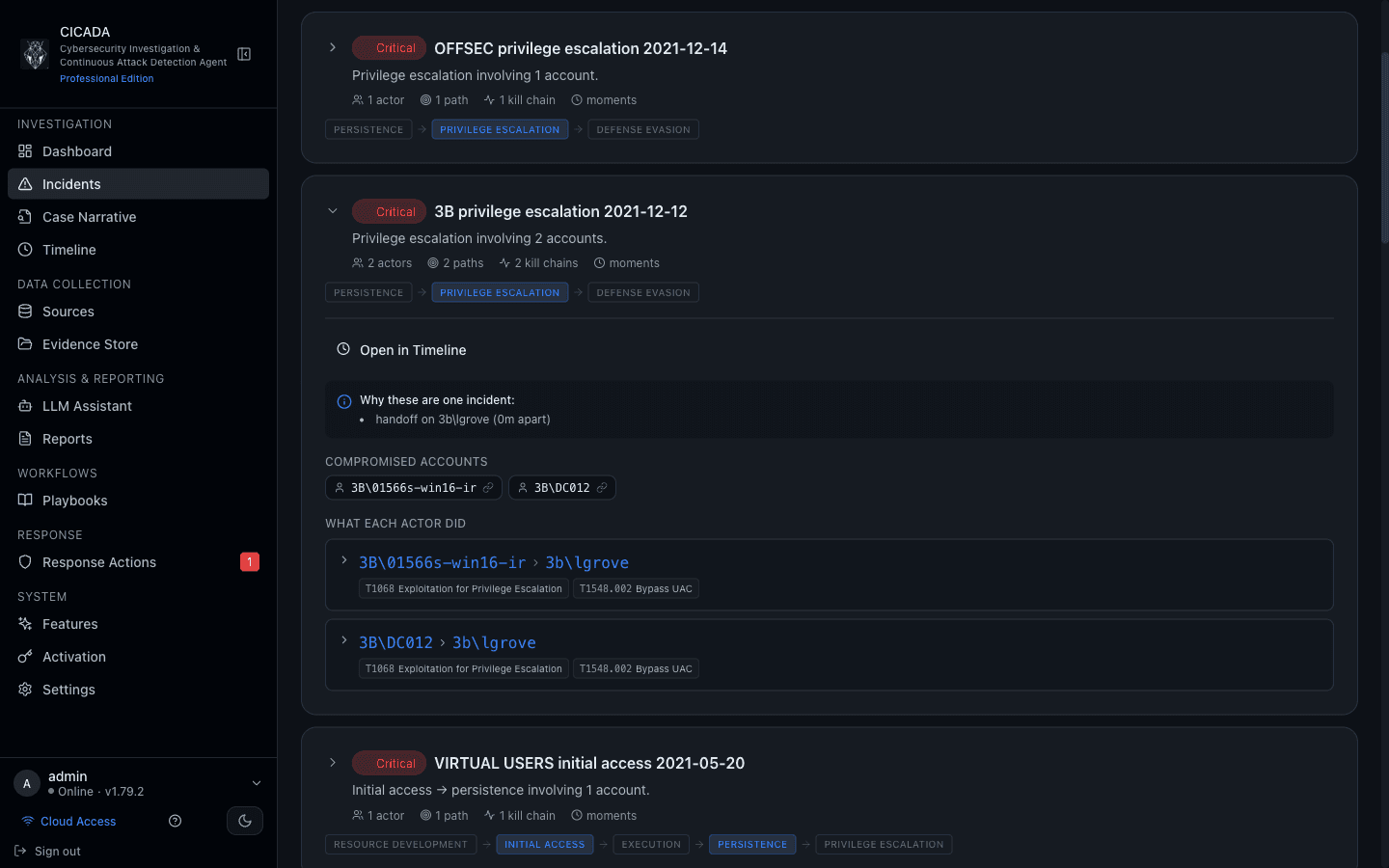
Four-Tier Scoring Engine That Catches What Your Team Would Miss.
Tier 1 signatures, Tier 2 multi-event sequences (YAML library, no code-release to tune), Tier 3 UEBA baselines, Tier 4 analyst flags. Hierarchical incidents group multi-actor kill chains automatically.
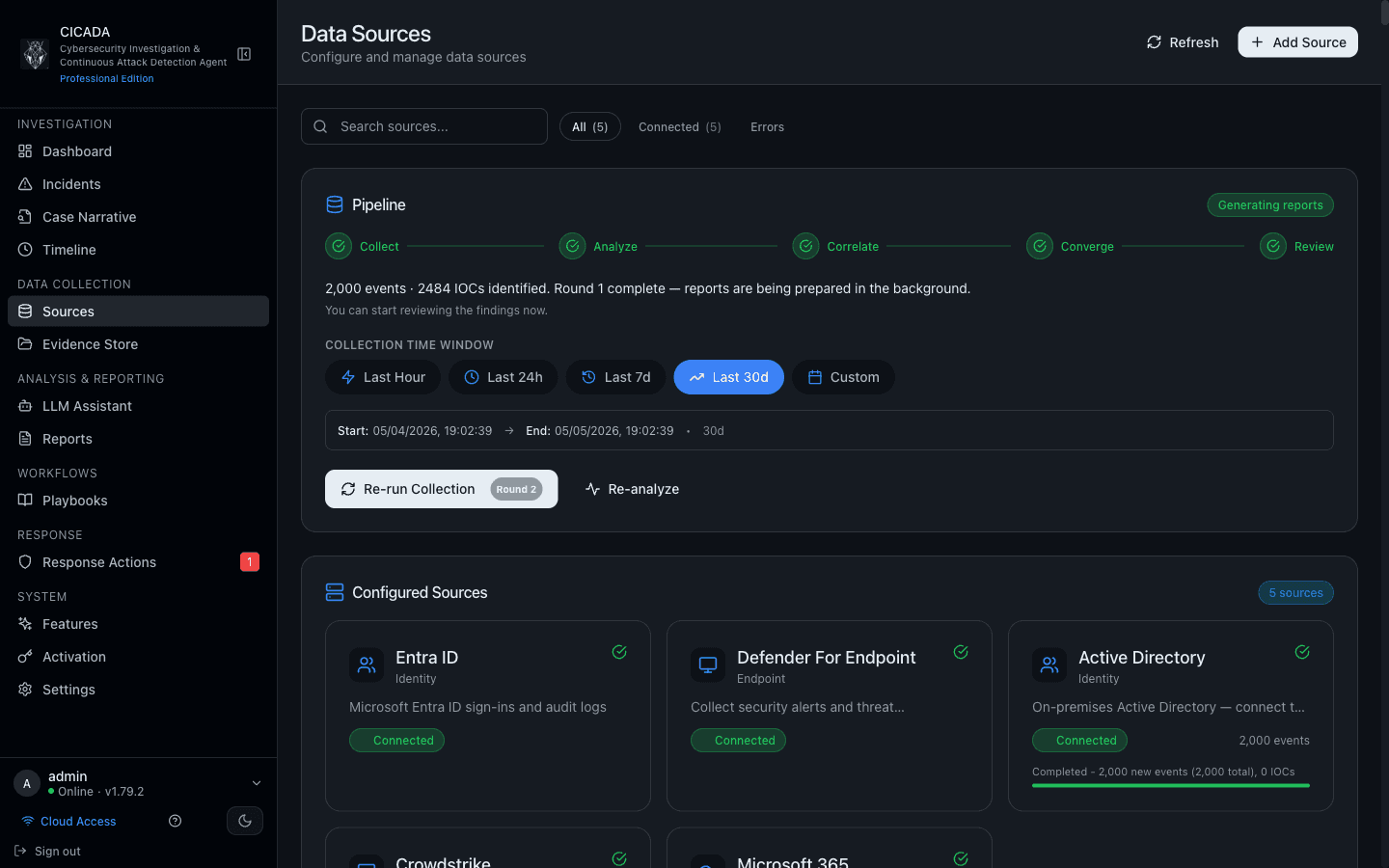
Five-Stage Pipeline From Collection to Review.
Collect → Analyze → Correlate → Converge → Review. Configurable collection time window. Read-only API access via the setup wizard for Entra, Defender, AD, CrowdStrike, and M365.
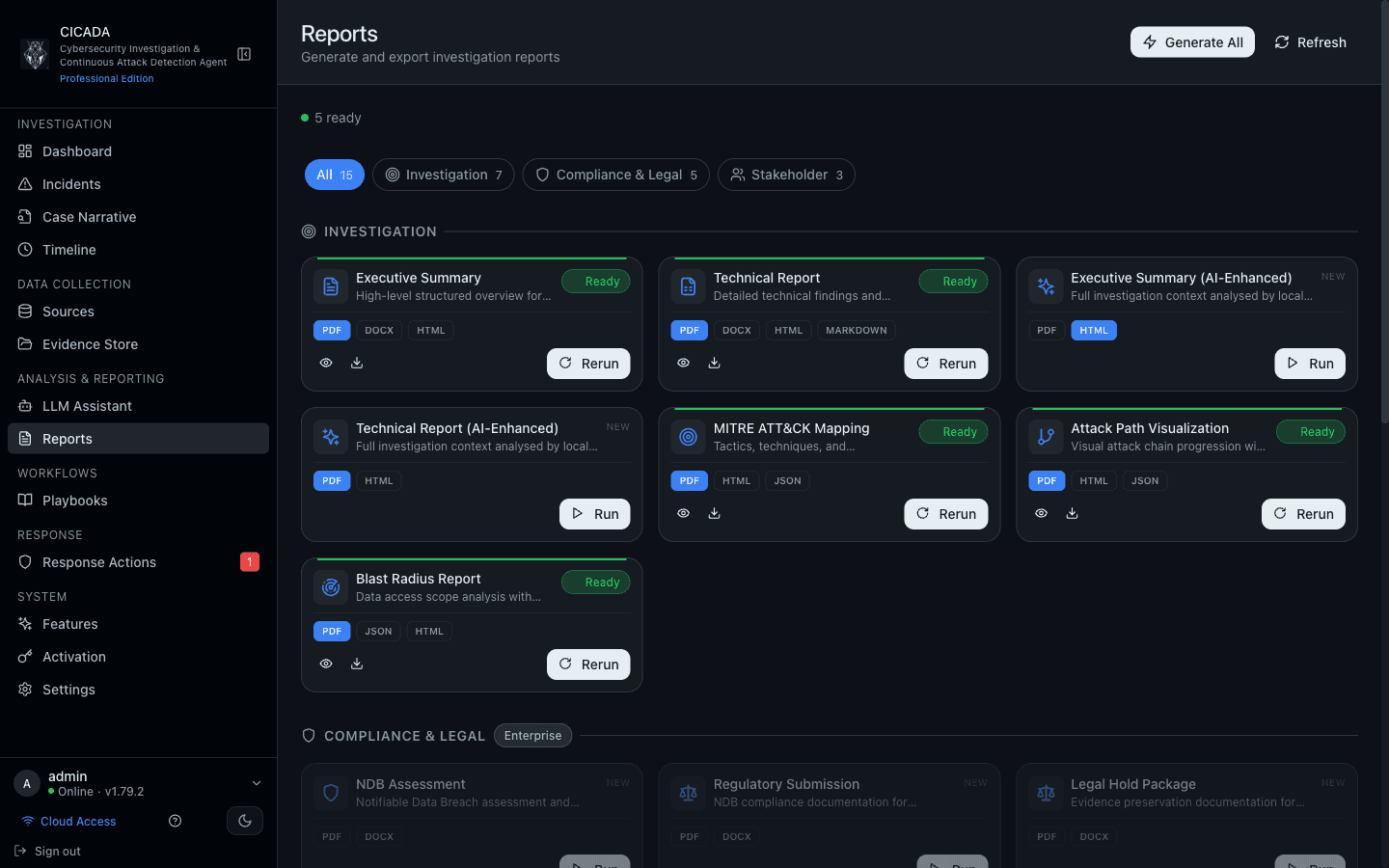
Executive, Technical, Compliance — Generated From Your Data.
15 report types across Investigation, Compliance & Legal, and Stakeholder categories. PDF, DOCX, HTML, JSON, Markdown. NDB Assessment, Legal Hold, Blast Radius, MITRE ATT&CK Mapping, and Attack Path Visualisation included.
Built for the stack you actually run.
Read-only API connections via the setup wizard. No agents to deploy.
Frequently asked questions
Where does my investigation data go?
How is CICADA IR priced?
How long does deployment take?
What support do you offer?
Can I upgrade from Community to Professional later?
Deploy in under 30 minutes.
One VM, three formats (OVA · QCOW2 · VHDX), agentless connection. Free Community Edition — full step-by-step in the Getting Started guide.